Microsoft February 2026 Patch Tuesday: 6 Exploited Zero‑Days + KEV Deadlines — How to Triage Fast
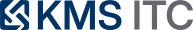
February’s Patch Tuesday includes six zero-days exploited in the wild, now tracked in CISA’s KEV. Here’s a practical triage pattern to patch the right systems first, validate quickly, and reduce blast radius while change windows catch up.
KMS ITC
February’s Microsoft security release isn’t a “nice to have” patch cycle.
It’s a measurable exploitation signal: multiple vulnerabilities are being actively used in the wild, and CISA has pulled them into Known Exploited Vulnerabilities (KEV) with a clear due‑date expectation.
Executive summary (3 bullets)
- Treat February 2026 as an incident‑adjacent patch week: Microsoft fixed six exploited zero‑days, and CISA KEV entries turn “patch soon” into “patch by a date.”
- Speed comes from triage discipline, not heroics: prioritise internet‑facing + high‑privilege + remote access / document entry points, then deploy in rings.
- Verification is part of the patch: confirm coverage, validate security controls (Mark‑of‑the‑Web, macro handling, RDP hardening), and monitor for post‑patch crash/sign‑in anomalies.
What changed
Microsoft’s February 2026 Patch Tuesday addressed 61 vulnerabilities, including six zero‑days reported as exploited in the wild.
CISA subsequently listed the affected CVEs in the KEV catalog and set a due date (March 3, 2026) for multiple items—turning these into top‑tier prioritisation inputs.
Examples of the KEV‑tracked Microsoft CVEs called out in February include:
- CVE‑2026‑21519 (Desktop Window Manager, elevation of privilege)
- CVE‑2026‑21533 (Remote Desktop Services, elevation of privilege)
- CVE‑2026‑21514 (Microsoft Word, security feature bypass)
- CVE‑2026‑21510 (Windows Shell, security feature bypass)
- CVE‑2026‑21513 (MSHTML/Trident framework, security feature bypass)
Why it matters
“Exploited in the wild” is the signal that changes the math:
- Attackers already have working paths. You’re not betting against theory; you’re racing a playbook.
- Patch gaps become targeting criteria. When exploit code exists, scanning and opportunistic compromise scale quickly.
- Entry points are operationally messy. Document handlers (Word), shell interactions, remote desktop components, and legacy web engines (MSHTML) tend to have wide footprint and complex dependency chains.
For security and IT leaders, the real risk isn’t just one CVE.
It’s the pattern:
- endpoints/server roles with high privilege surface
- inconsistent patch rings or stalled change windows
- incomplete coverage validation
- attackers pivoting from “one foothold” to “business impact”
What to do (copy/paste checklist)
1) Scope the blast radius (today)
- Pull an asset list for: Windows endpoints, RDS hosts, jump boxes, VDI images, Office installs (including shared/RDS session hosts).
- Identify systems that are internet‑facing (directly or via exposed gateways) and systems that are privilege amplifiers (admin workstations, identity‑adjacent servers).
- Confirm whether the KEV‑tracked CVEs apply to your versions/roles (vendor guidance + patch notes).
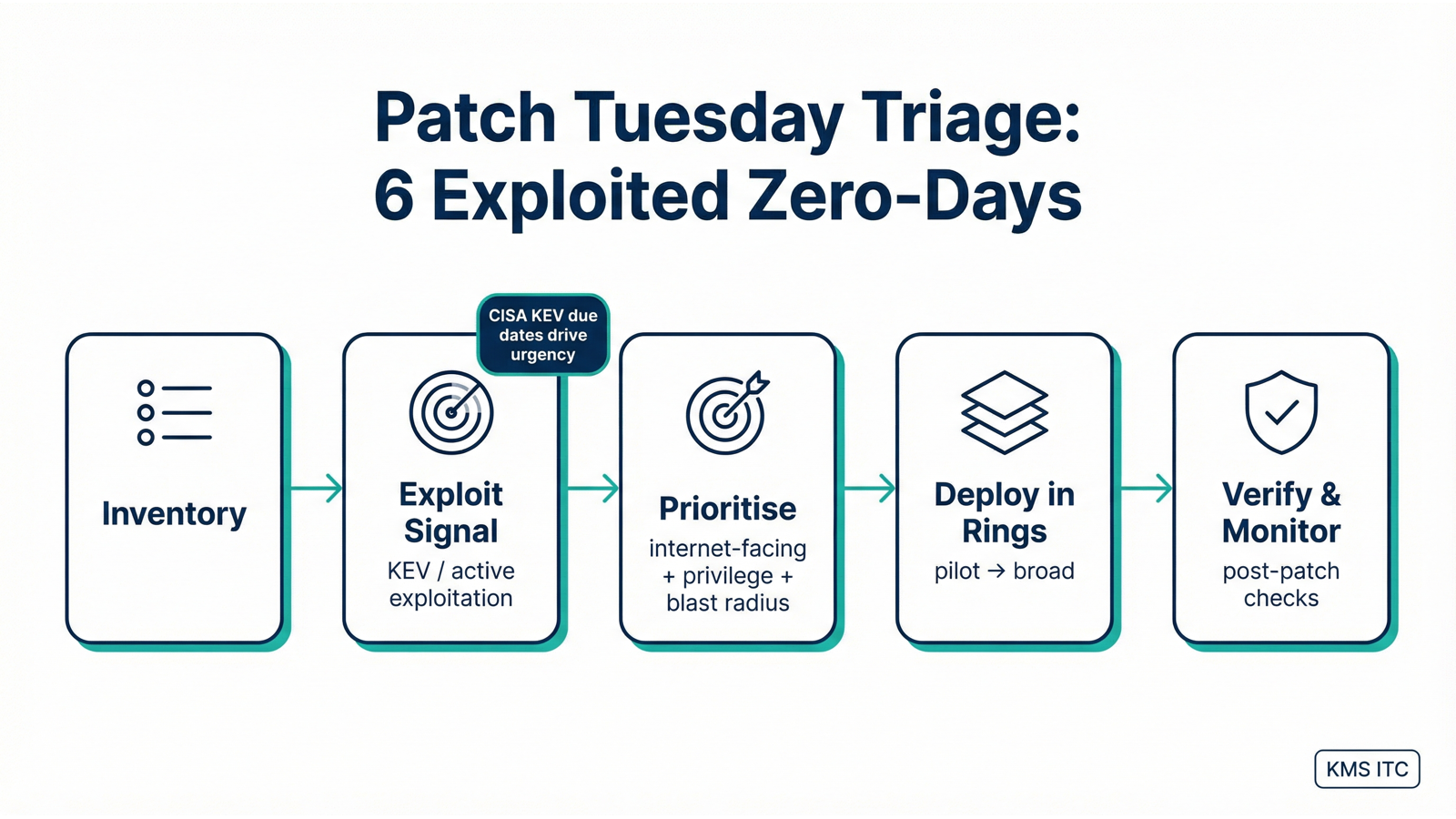
2) Set a simple prioritisation rule (today)
- Top priority (24–72h): KEV + internet‑facing OR KEV on admin endpoints/jump hosts.
- Next priority: KEV + internal‑only but high‑privilege footprint (RDS, shared session hosts, gold images).
- Normal cadence: non‑KEV items (unless they affect exposed edge services or critical identity paths).
3) Deploy in rings (this week)
- Ring 0: security/IT pilot group + representative server role sample.
- Ring 1: high‑risk populations (admins, RDS/jump hosts, devices with privileged tooling).
- Ring 2: broad endpoint fleet.
- If you use imaging/VDI: patch gold images first, then rebuild pools.
4) Validate and monitor (don’t skip this)
- Confirm patch coverage with a second signal (endpoint management + vulnerability scanner + spot checks).
- Verify “guardrails” still work: Mark‑of‑the‑Web behaviour, Office protected view expectations, macro policy enforcement.
- Monitor: authentication anomalies, RDP service restarts, unusual Word/Explorer crashes, and endpoint protection telemetry changes.
Risks / tradeoffs
- Patching fast can break workflows. Remote desktop and Office updates are notorious for edge cases; ring deployments reduce the risk of an org‑wide outage.
- Hard deadlines create perverse incentives. “Patch everything everywhere” often fails; targeted KEV triage usually patches more effectively under time pressure.
- KEV is not your only priority input. If you’re heavily cloud/SaaS or have unusual exposure (kiosks, OT jump hosts, partners), adjust the matrix—but keep the rule simple enough to execute.
Sources
- Qualys — Microsoft and Adobe Patch Tuesday, February 2026 Security Update Review
- CISA — Known Exploited Vulnerabilities (KEV) Catalog
- Microsoft MSRC — CVE‑2026‑21519
- Microsoft MSRC — CVE‑2026‑21533
- Microsoft MSRC — CVE‑2026‑21514
If you’re deciding what to do next, map your biggest pain (patching speed, exposure reduction, validation confidence) to the controls/patterns above—then pilot a lightweight version on one initiative.