n8n Expression Escape → RCE (CVE-2026-25049): Patch Fast, Then Contain
A critical n8n expression-sandbox escape can turn ‘workflow author’ access into server-level command execution. Here’s what changed, why it matters, and a practical hardening checklist.
KMS ITC
Workflow automation is supposed to remove toil. But when the automation engine can run code paths you didn’t intend, it becomes a control plane risk.
This week, n8n disclosed CVE-2026-25049 (critical) — an expression escape issue that can allow system command execution on self-hosted instances under certain permissions. The uncomfortable part: n8n is often sitting on your most valuable credentials.
1) Executive summary
- Treat this like a control-plane vulnerability. If an attacker can author/modify workflows, they may be able to jump to host-level command execution.
- Patch is the priority. Upgrade to n8n 2.5.2+ or 1.123.17+ (then review other same-day advisories).
- Hardening still matters after patching. Constrain who can create/edit workflows, isolate the runtime, and tighten webhook exposure to reduce blast radius.
2) What changed
n8n patched additional exploits in its expression evaluation system following the earlier CVE-2025-68613.
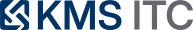
In CVE-2026-25049, an authenticated user with permission to create or modify workflows could abuse crafted expressions to trigger unintended system command execution on the host running n8n.
- Fixed in: n8n 1.123.17 and 2.5.2 (and later).
3) Why it matters
n8n isn’t “just another web app.” In many environments it is:
- a credential hub (API keys, OAuth tokens, DB creds, cloud keys)
- a network pivot (connectors to internal services and third parties)
- a workflow trigger surface (webhooks, schedules, inbox-style events)
That combination creates a classic high-impact pattern:
- low-to-medium privilege in the app (workflow author)
- becomes high privilege on the host (RCE)
- which becomes high privilege everywhere (credential theft + lateral movement)
Even if your instance is “internal only,” many teams expose at least some workflows via webhooks. If webhook endpoints can be hit broadly, the operational stakes go up fast.
4) What to do (checklist)
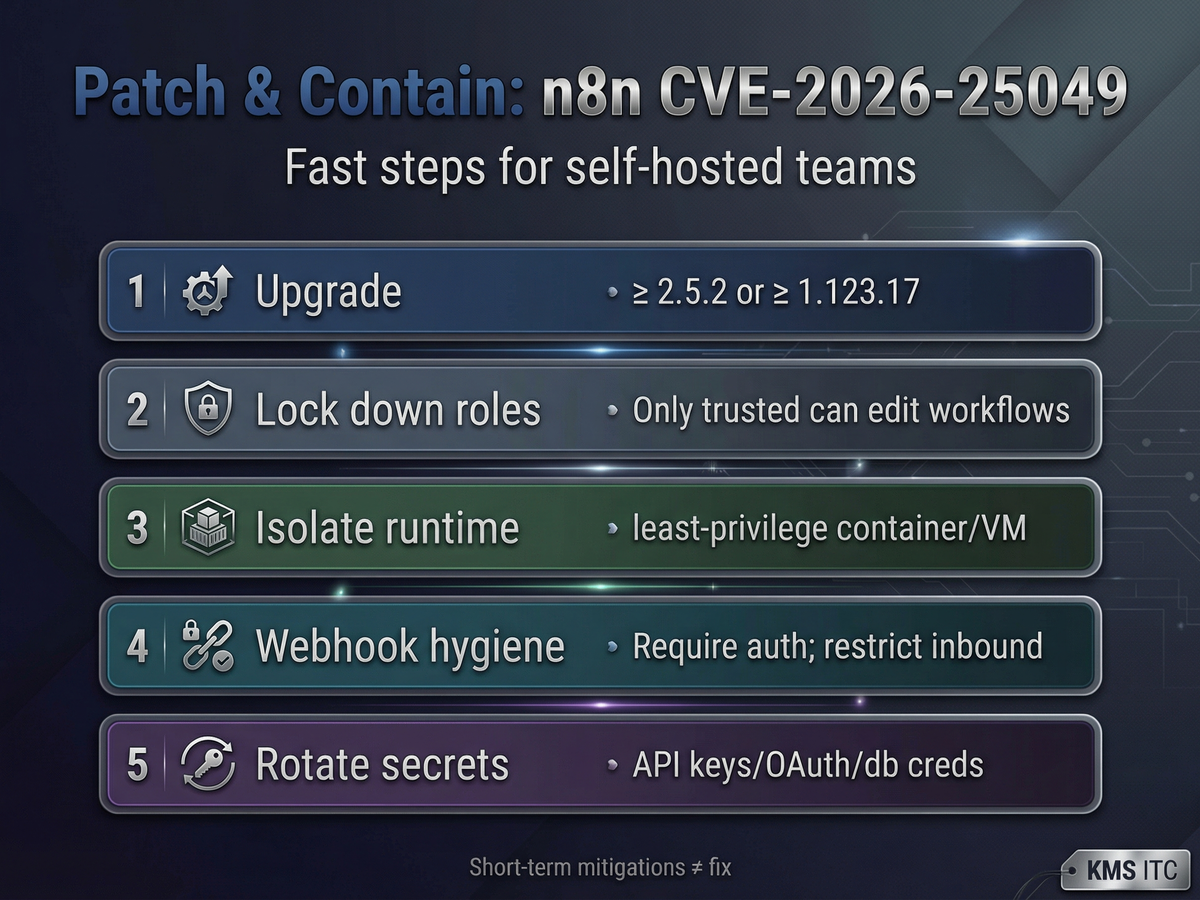
4.1 Patch immediately (the actual fix)
- Upgrade to 2.5.2+ (current major) or 1.123.17+ (older line), then redeploy.
- If you pin container images, rotate the tag to a known good digest and record it.
4.2 Reduce who can author workflows
- Restrict workflow creation/editing to fully trusted users only.
- Review role bindings and any SSO/group mappings that accidentally grant editor access.
4.3 Contain the runtime (assume compromise)
- Run n8n in a hardened container/VM with:
- least-privilege OS user
- read-only filesystem where possible
- tight egress (only what workflows require)
- no access to Docker socket / host mounts
4.4 Webhook hygiene
- Require auth on public webhooks (or put them behind an API gateway).
- Restrict inbound (allowlists, WAF rules, rate limits) where feasible.
- Audit which workflows expose webhooks and whether they need to be public.
4.5 Rotate secrets (because you can’t prove they weren’t read)
- Rotate n8n-stored credentials that can reach:
- cloud IAM keys
- production databases
- CI/CD tokens
- “god-mode” SaaS admin keys
5) Risks / tradeoffs
- Patching fast can break workflows. Some teams rely on expression edge cases. Test critical workflows, but don’t “test forever.” Timebox validation.
- Locking down editors slows iteration. That’s the tradeoff: you’re protecting a control plane. Use approvals and change windows if needed.
- Hardening reduces convenience. Tight egress and minimal permissions can reveal hidden coupling (workflows that quietly depend on broad network access). That’s good to discover—plan the work.
Sources
- n8n security advisory (GHSA-6cqr-8cfr-67f8 / CVE-2026-25049): https://github.com/n8n-io/n8n/security/advisories/GHSA-6cqr-8cfr-67f8
- Endor Labs analysis (type confusion → sanitizer bypass): https://www.endorlabs.com/learn/cve-2026-25049-n8n-rce
- The Hacker News roundup / impact context: https://thehackernews.com/2026/02/critical-n8n-flaw-cve-2026-25049.html
- SecureLayer7 technical write-up (webhook exposure scenario): https://blog.securelayer7.net/cve-2026-25049/